A very effective service that substantially simplifies the log management process. The various dashboards are very comprehensive and provide easy access to information.
Information Security Officer, AXA Partners
- Services
-
Solutions
- Solutions
- Fraud Prevention
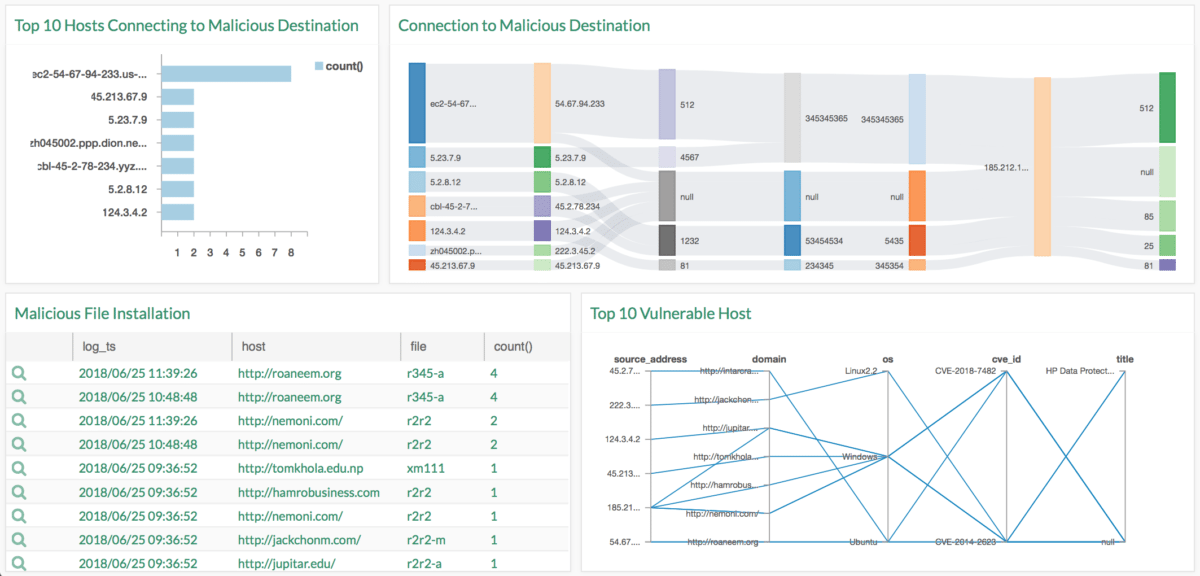
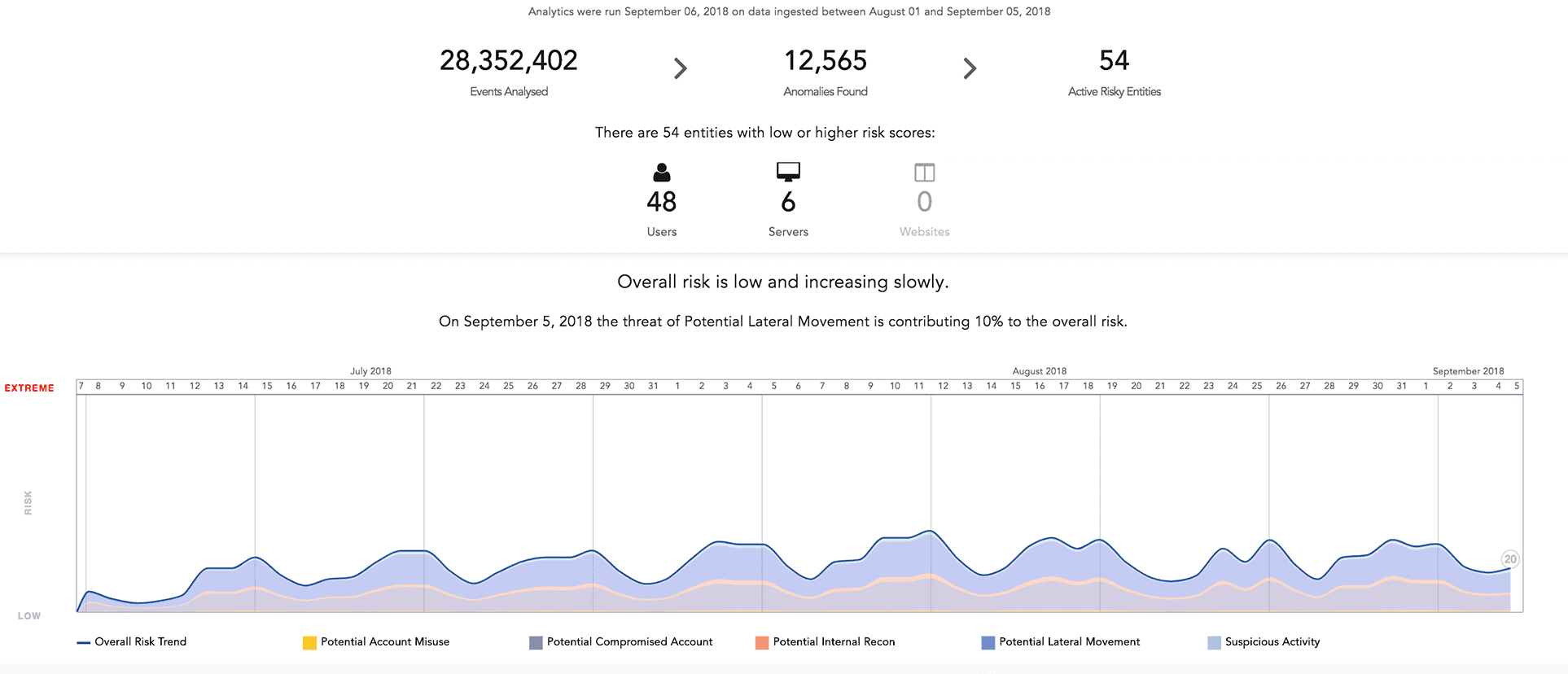
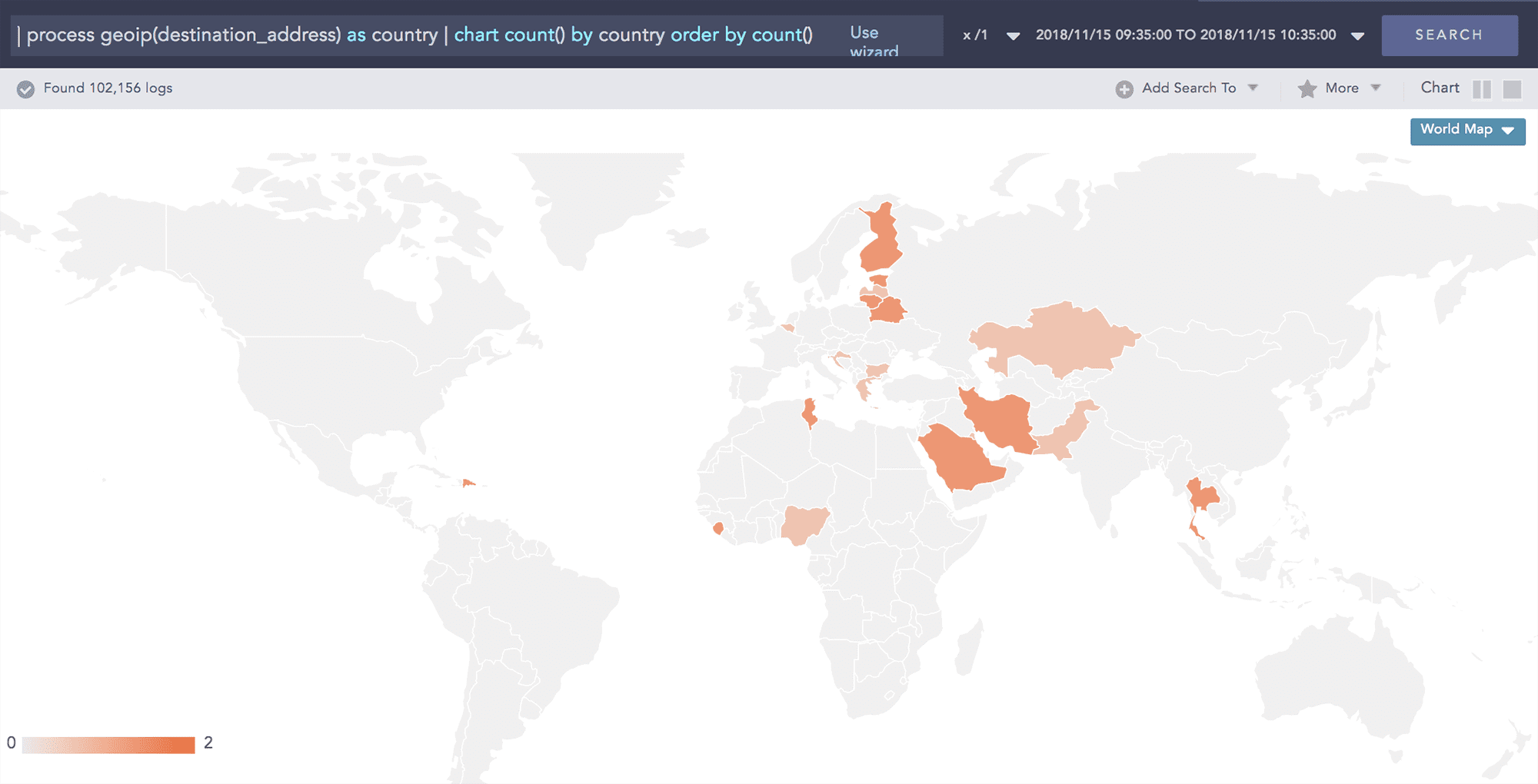
- Threat Detection & Response
- Identity & Access Management
- Information Protection
- Internet Of Things (IoT) Security

Our IoT security solutions unlock business value by enabling secure access to IoT data.
read more
Cyber Security Solutions
Our Cyber Security Solutions deal with challenging aspects such as fraud prevention, threat detection & response, identity & access management, IoT security, cloud security and information protection, among others.
read more -
Managed Security
- Managed Security
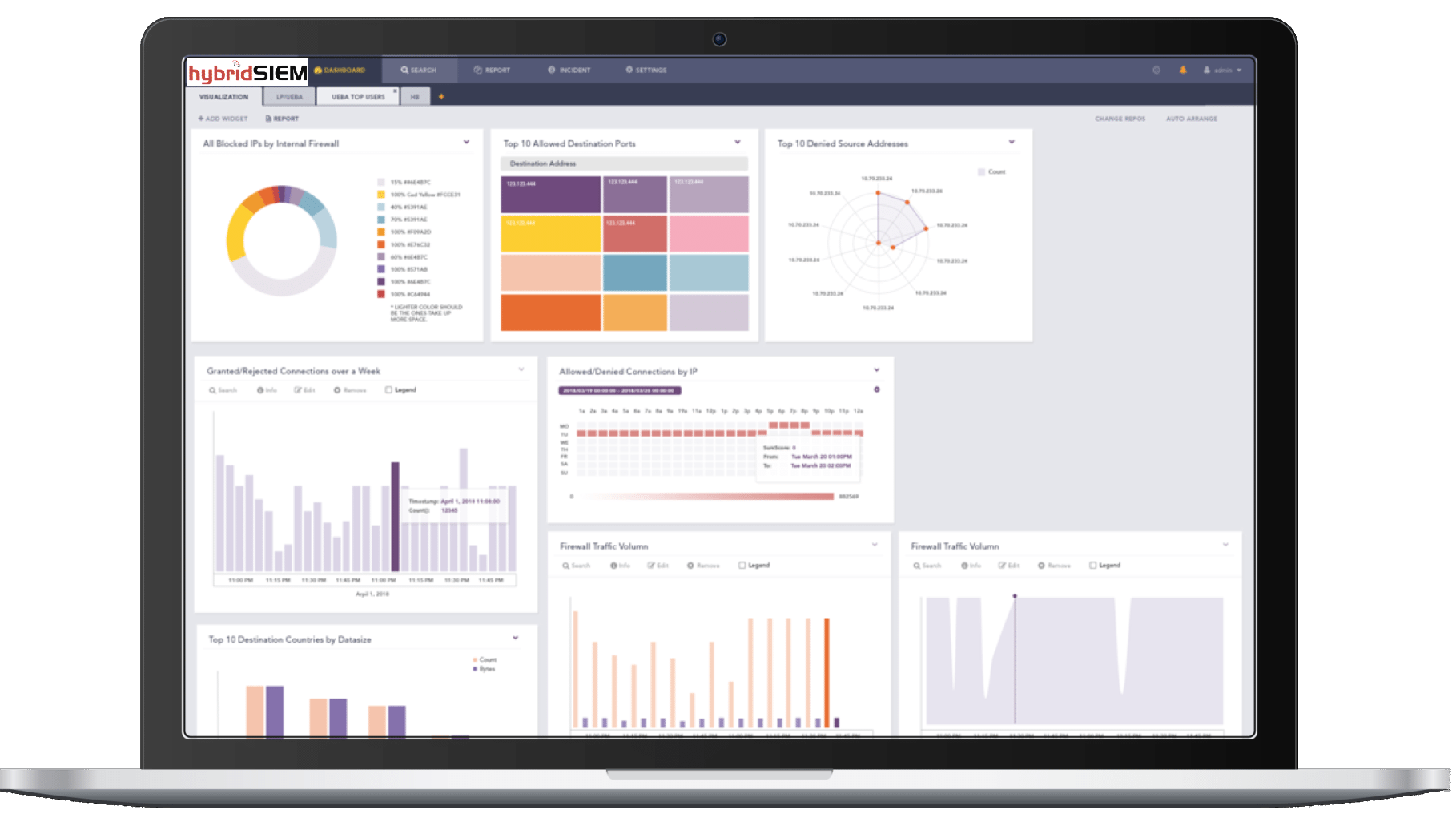
- HybridSIEM

HybridSIEM - Next Generation SIEM Service
read more - Connectivity
- Web Applications
Managed Security Services
Our Managed Security Services strengthen our customers cyber defense programs often at a fraction of the cost of in-house security resources utilizing BesecureCloud big data and supercomputing capabilities.
read more -
Education
- Education
- Information Security Training
- ISO 27001 Certification
- Risk Management Training
- Business Continuity Training
-
Security Awareness
A training program for security awareness will inspire and encourage everyone to practice secure computing because everyone - from management to end users - will understand that they have a vested interest in secure computing.
read more
Education
Comprehensive vendor-neutral business continuity, information security, ISO 27001, risk management certification on-premise or e-learning training courses and awareness briefings for executive management, security and system administrators and corporate users.
read more -
Certificates
- Certificates
Certificates
Entrust Datacard is one of the most trusted brands in online security with one of the most respected client bases, empowering governments, enterprises and financial institutions in more than 5,000 organizations spanning 150 countries.
read more - Events
-
About Us
- About Us
About Us
We are a leading provider of Governance, Risk & Compliance (GRC) services, Cyber Security solutions, Managed Security services, Certification Training and Awareness programs, trusted by global organizations across telecommunication, financial services, energy industries and other medium - large enterprises.
read more